The Gorgon Defender App
Full visibility and control over your network security — from anywhere. Monitor threats, manage decoys, and respond to incidents in real time across all your devices.
Full visibility and control over your network security — from anywhere. Monitor threats, manage decoys, and respond to incidents in real time across all your devices.
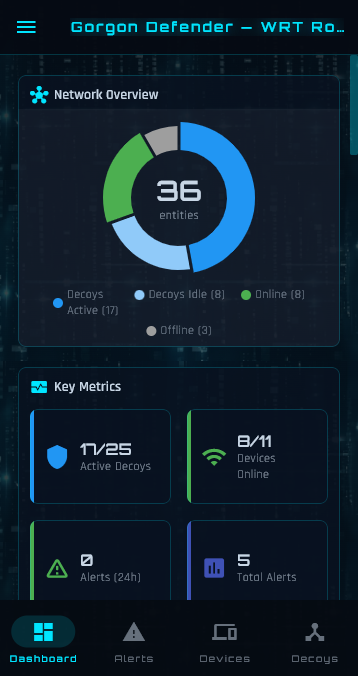
The dashboard gives you an instant overview of your network's security posture — decoy coverage, device status, alert trends, and live packet activity — all in one place.

Enter edit mode to drag-and-drop cards into any arrangement. Add widgets, remove ones you don't need, rename titles, and reset to defaults — your layout saves automatically.
Real-time detection of port scans, network reconnaissance, and unauthorised access attempts — with intelligent classification and instant push notifications.
Alerts are automatically classified by severity: informational (new devices), warnings (first decoy contact), and critical scan detection (port scans, network sweeps, ARP scans). Each tier has distinct colour coding for at-a-glance triage.
Receive instant push notifications the moment a threat is detected. Configure per-severity filtering so you only get alerted on what matters to you — informational events, warnings, or critical scans.
When a new threat is detected while you're using the app, a full-screen pulsing overlay immediately captures your attention with threat details. Tap to dismiss and navigate directly to the relevant alert.
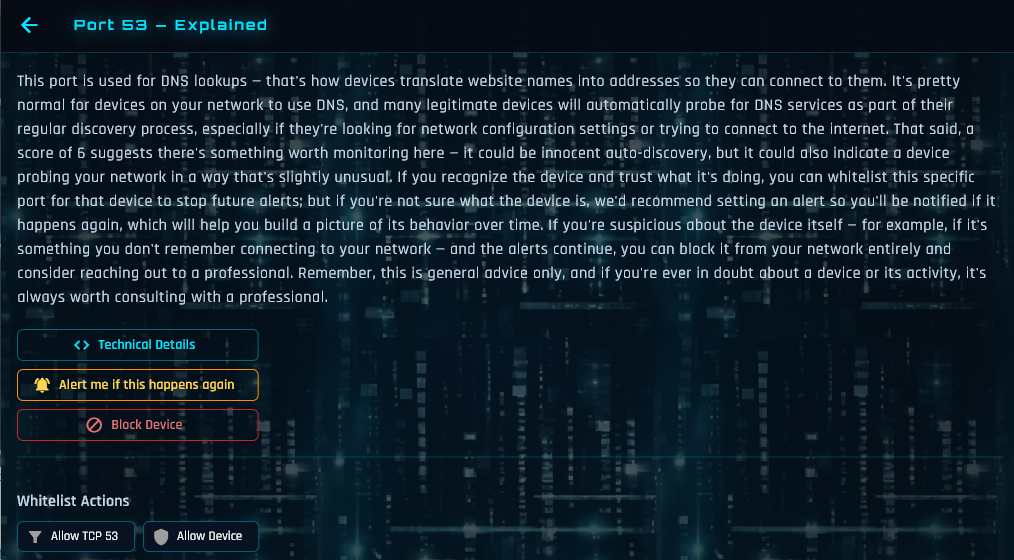
Don't just see alerts — understand them. Every suspicious port contact comes with a detailed, plain-language explanation telling you exactly what the activity means, why it matters, and what to do about it.
Deploy ghost honeypot hosts that are invisible to legitimate users but irresistible to attackers. Any contact is a guaranteed threat indicator.
Create honeypot hosts with unique MAC addresses, DHCP-assigned IPs, and realistic hostnames. They appear as genuine devices to attackers but generate zero false positives — any contact is a confirmed threat.
Decoys can mimic real devices on your network — copying their hostname, vendor signature, and DHCP fingerprint. Attackers cannot distinguish decoys from genuine hosts.
Enable autonomous decoy management and the system will automatically create, position, and schedule decoys based on your network's activity patterns — no manual configuration needed.
Know every device on your network, its behaviour patterns, and exactly when something changes.
Automatic passive discovery via ARP, DHCP, mDNS, SSDP, NBNS, and LLMNR. Every device on your network is identified with its MAC address, IP, hostname, and hardware vendor.
A 7-day by 24-hour activity heatmap for every device shows when it's typically active. Understand usage patterns and spot anomalous after-hours activity at a glance.
Block suspicious devices with a single tap. Choose internet-only blocking (device stays on LAN but loses WAN access) or full network isolation for complete quarantine.

Extend your corporate security perimeter to employee home offices. Built-in SIEM integration forwards alerts to your SOC in real time — with full context about which site, employee, and location is affected.
Monitor and manage your network from anywhere in the world with end-to-end encrypted tunnelling and flexible access sharing.
Remote access uses a TLS-over-WebSocket tunnel through our cloud relay. The relay is a blind pipe — it cannot read your traffic. Two-factor authentication with serial number and relay secret.
Share access securely with family members or IT administrators. Generate a short code that grants remote access. Codes expire after 24 hours and are automatically consumed after use.
Every remote login is recorded with IP address, GPS coordinates, and reverse-geocoded location. View login locations on an interactive map — know who accessed your network and from where.

A polished, adaptable experience that fits your brand, your language, and your users. Every string in the app is translatable, and the entire UI adapts to right-to-left scripts.
Keep every deployed device up to date — securely and automatically.
Firmware updates are delivered via secure cloud infrastructure with SHA-256 verification. The app shows release notes, tracks progress, and automatically rolls back on failure.
The app automatically detects outdated router firmware and guides users through the update process. Semantic API versioning ensures the app gracefully adapts to both older and newer server versions.